Mobile Threat Report
This project was really fun. It was a stimulating challenge, the best kind. How to make complex, obscure data relatable, understandable, and accessible. I’ve been interested in information architecture since I began studying design, a combination between entering RISD in the same year as John Maeda, and taking courses with renowned professor, Kris Lenk.

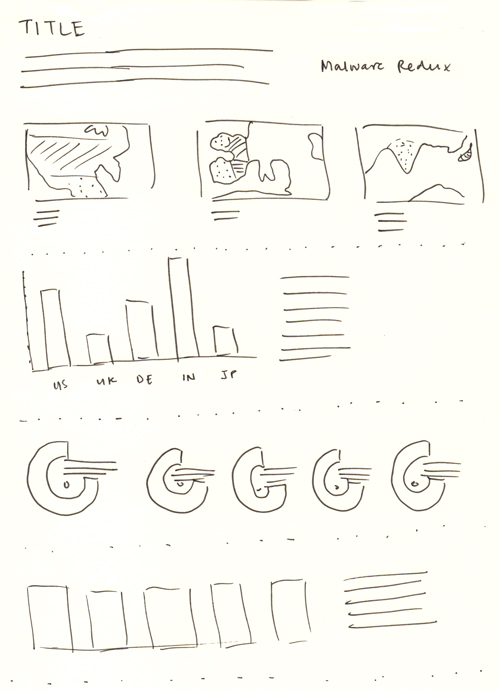
Working directly with the Lookout security, data, and PR teams, we came up with a series of relevant content to articulate the various types of threats that can plague android devices around the world. We focused on just five countries, with the most complete data sets, to create the big picture. I began by sketching out various concepts around how to portray the threats in context against each other, as well as explain the implications of each one.
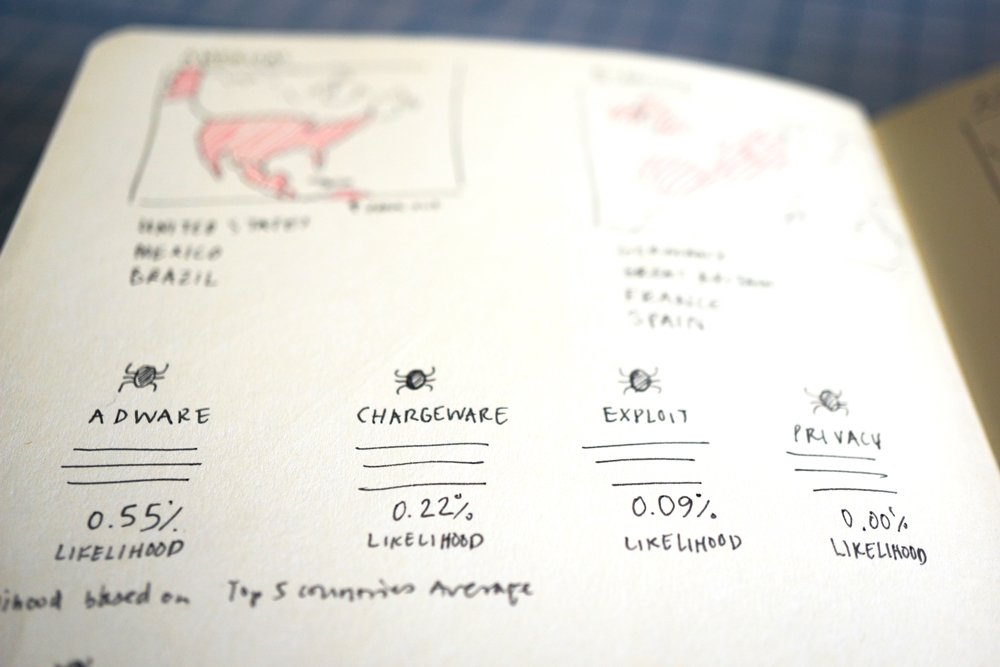
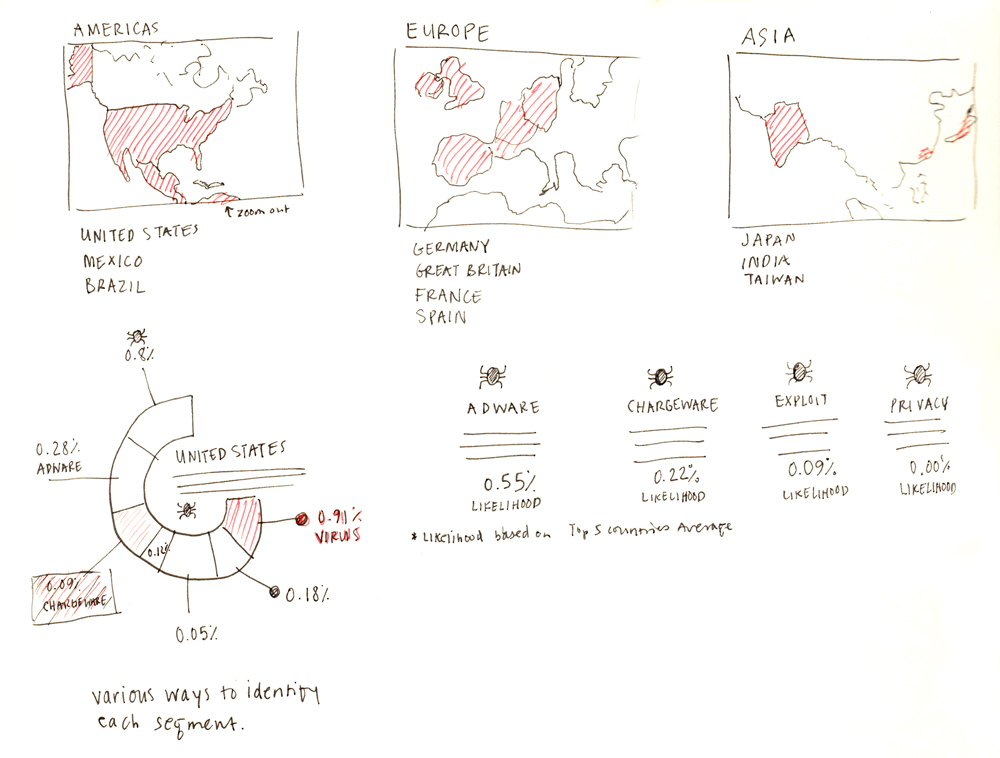
From the outset, the security team wanted to explain nine different kinds of threats. Typically, the layman term is virus, but once you dive deeper into the subject, it becomes apparent there are so many different threats that virus is not really an all-encompassing or appropriate word. Lookout’s term of choice is malware but this is still very broad and vague. The most common type of threat is called adware, which is software that maliciously collects your personal information while posing as an innocent advertising platform within another app. Another kind, chargeware, is responsible for unexplained fees and charges, most commonly when downloading a third party application instead of one of approved official sources.
As you can see in this early draft, above, the problem with explaining nine different kinds of mobile threats, aside from the audience’s attention span, is clarity. It became very difficult to differentiate between them and keep track of which data piece belonged to which part of the graph. After some discussion, I persuaded the team to narrow it down to only five, which both strengthened the clarity of the message, and made the charts easier to comprehend.
The final piece was localized in several languages and published in all sorts of news related to protecting one’s mobile device. Beginning with a clear overview and context for why the reader should learn about mobile threats, then diving into detail with rich comparisons between each country, which provides insight on the unique mobile marketplaces.
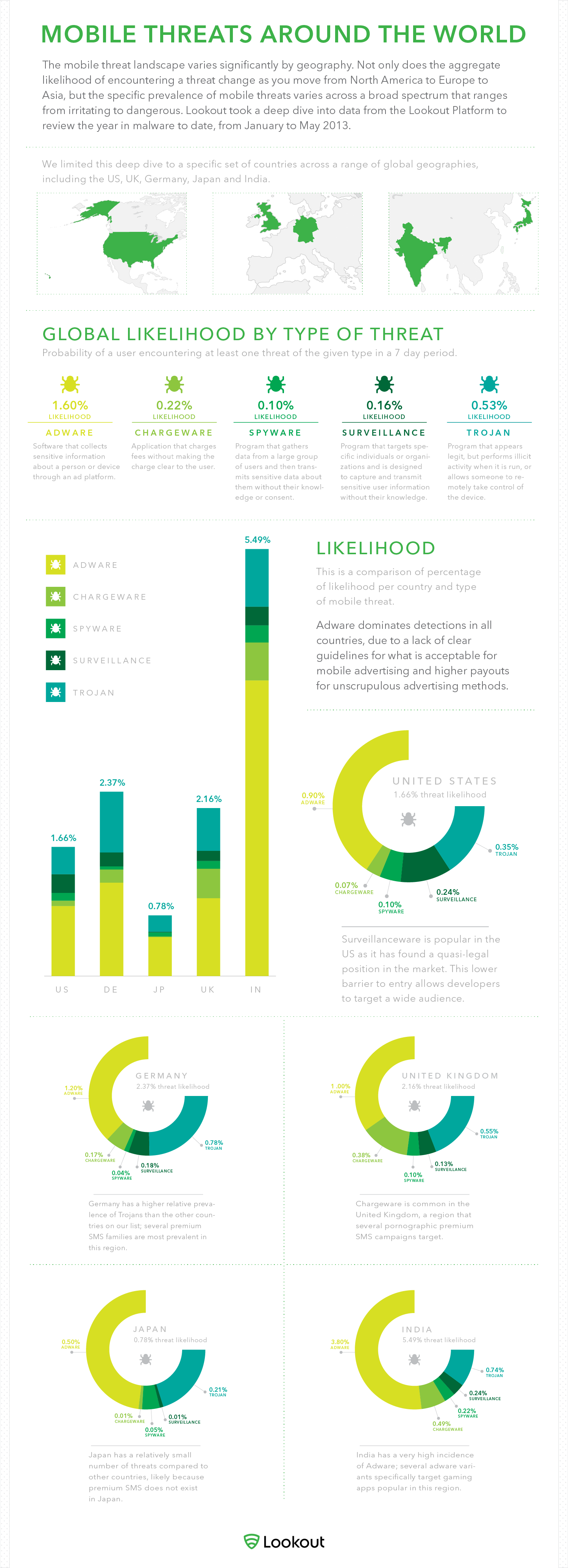
Featured in articles across Business Insider, LA Times, Android Guys, PC MAG: Security Watch, and FR:Android (Android France), among others. Localized in UK English, German, French, and Japanese.